Automatically find mobile app vulnerabilities that are really exploitable
Automatically find mobile app vulnerabilities that are really exploitable
Test every layer of your mobile app with deep security analysis and compliance checks built into every release
Test every layer of your mobile app with deep security analysis and compliance checks built into every release




Built by the world's leading mobile security expert, Sergey Toshin. $1M+ earned in bounties
Ranked #1 in Samsung's mobile vulnerability detection program
#1 researcher in Google Play Security Reward Program
186 CVEs + 156 bounty findings discovered across 165 global brands
Built by the world's leading mobile security expert, Sergey Toshin. $1M+ earned in bounties
Ranked #1 in Samsung's mobile vulnerability detection program
#1 researcher in Google Play Security Reward Program
186 CVEs + 156 bounty findings discovered across 165 global brands
Built by the world's leading mobile security expert, Sergey Toshin. $1M+ earned in bounties
Ranked #1 in Samsung's mobile vulnerability detection program
#1 researcher in Google Play Security Reward Program
186 CVEs + 156 bounty findings discovered across 165 global brands
Trusted by security teams at
Trusted by security teams at
Trusted by security teams at
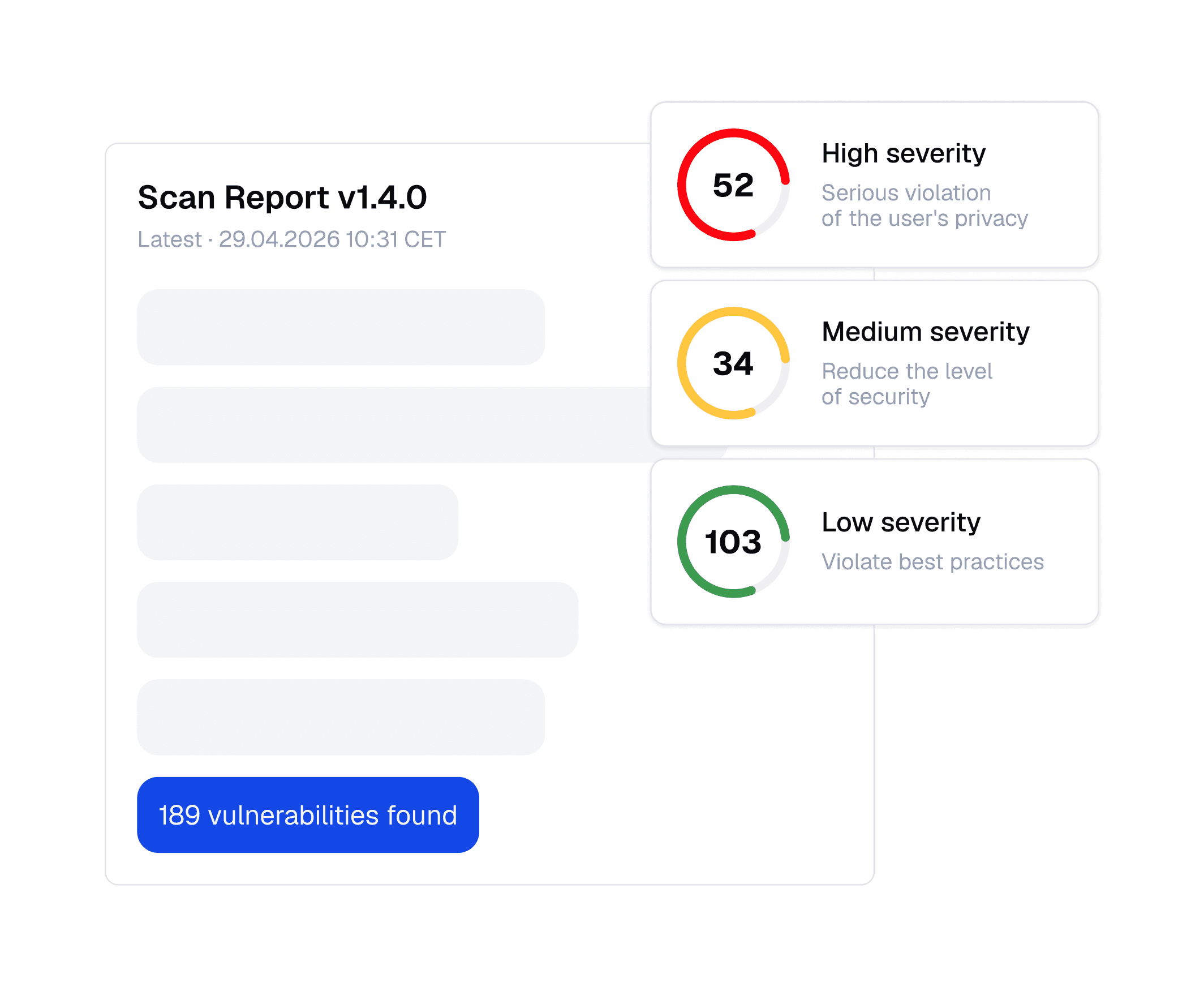
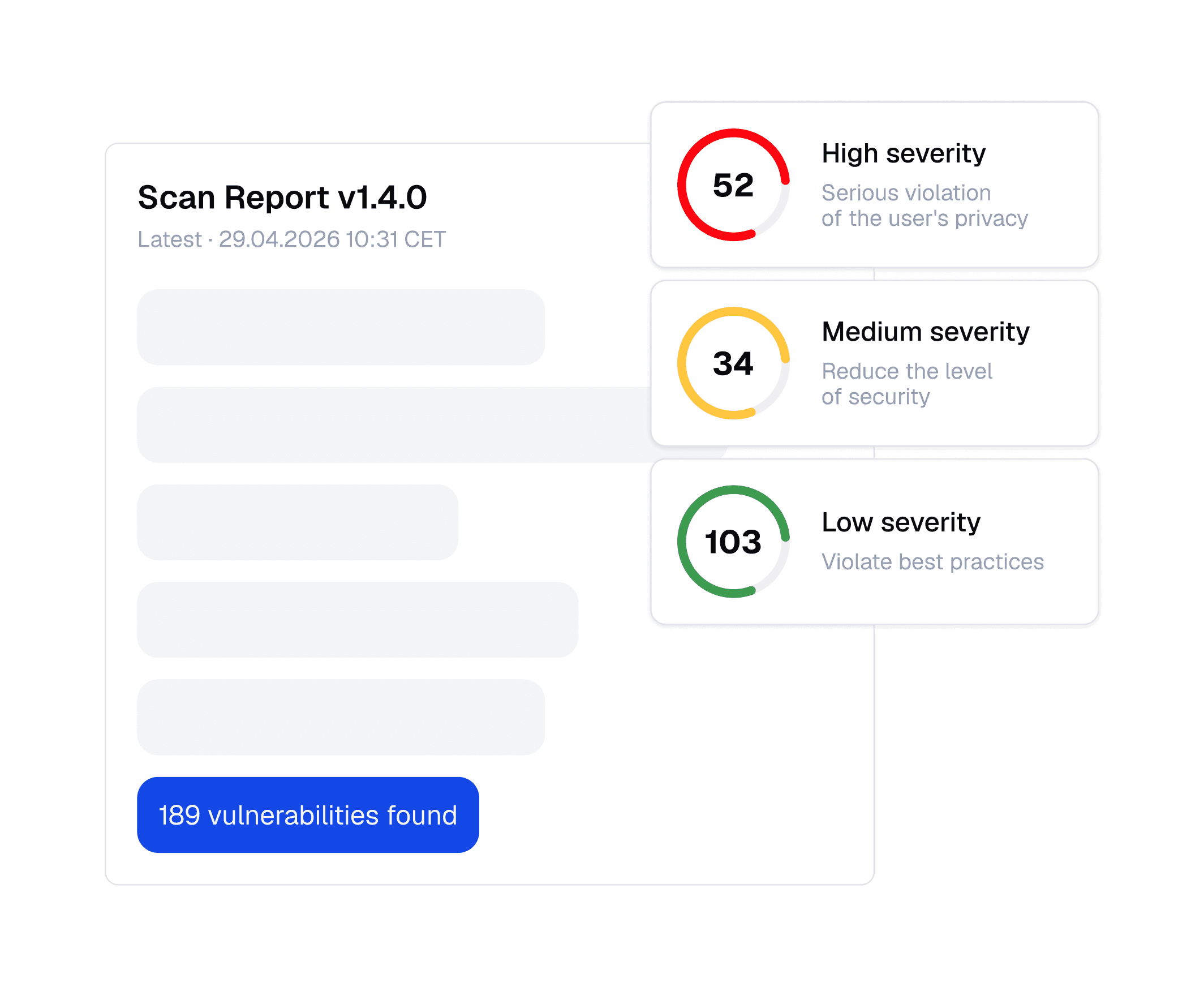
Not just "vulnerable" — but why, how, and what to do about it
Not just "vulnerable" — but why, how, and what to do about it
Most scanners tell you a vulnerability exists. Oversecured tells you what it means, how severe it is, and exactly how to fix it in language your developers can act on.
Most scanners tell you a vulnerability exists. Oversecured tells you what it means,
how severe it is, and exactly how to fix it in language your developers can act on.
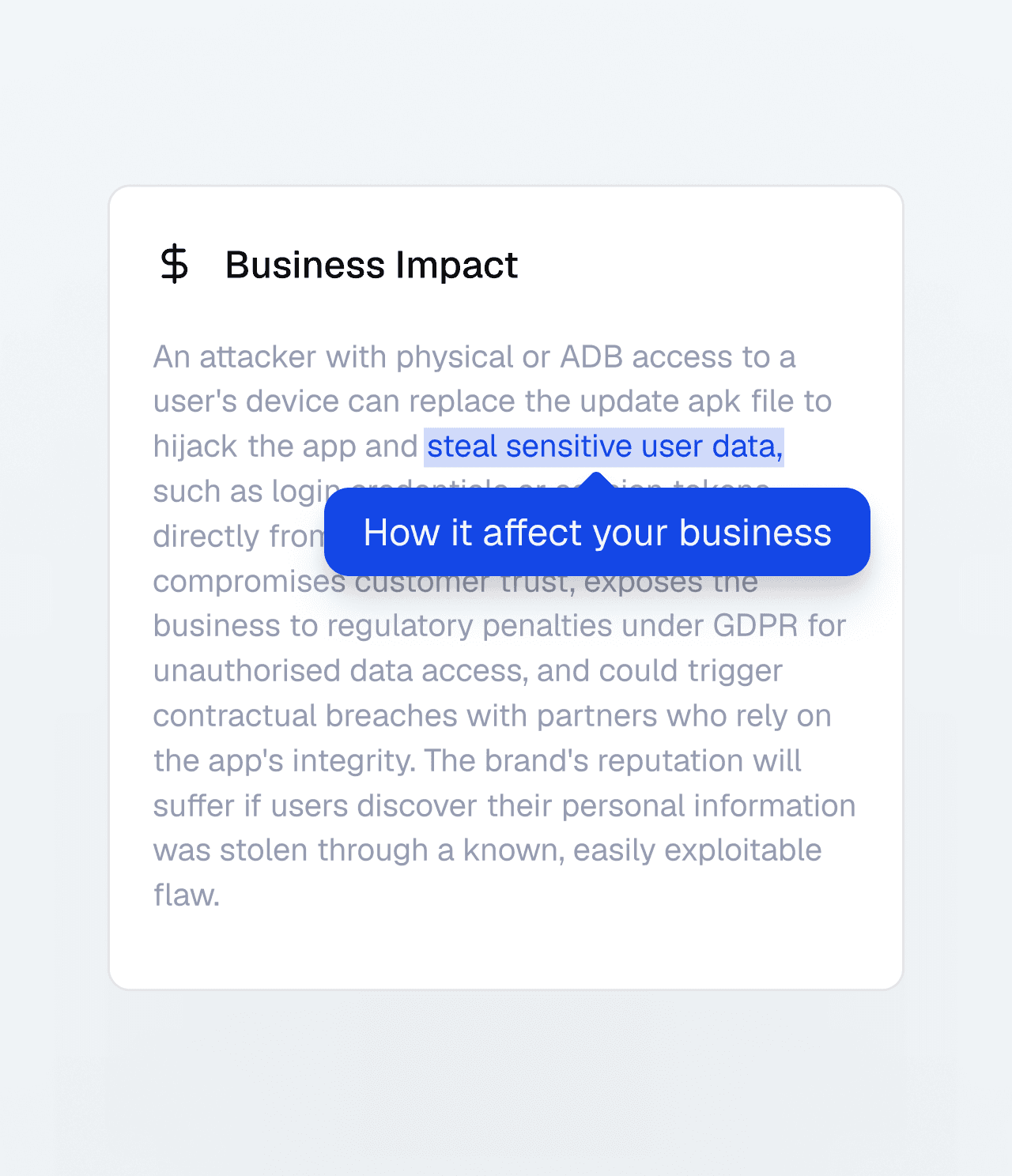
Business impact
What an attacker could achieve if this is exploited: data theft, account takeover, financial loss
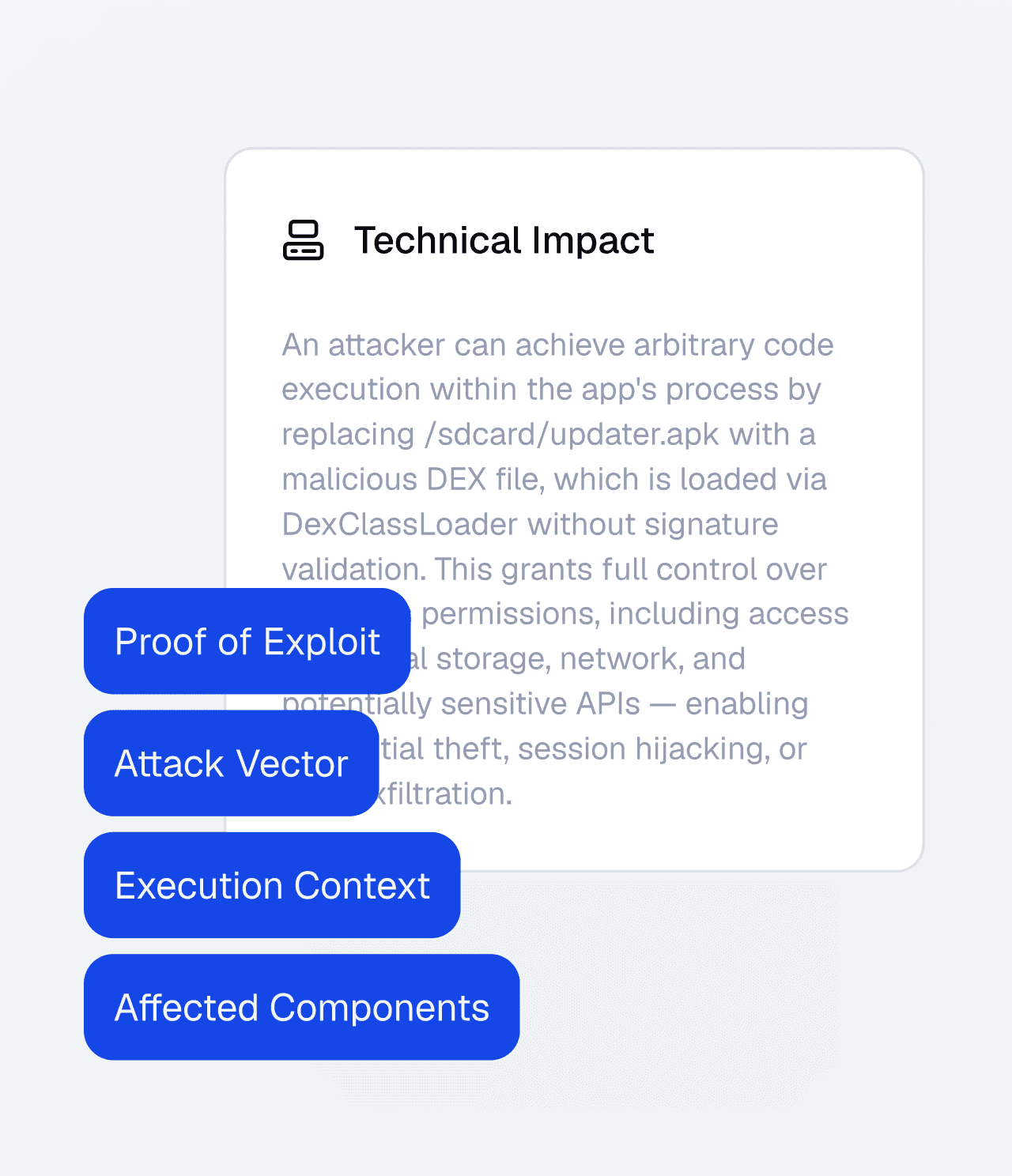
Technical impact
What happens at the system level: which data is exposed, which operations are affected
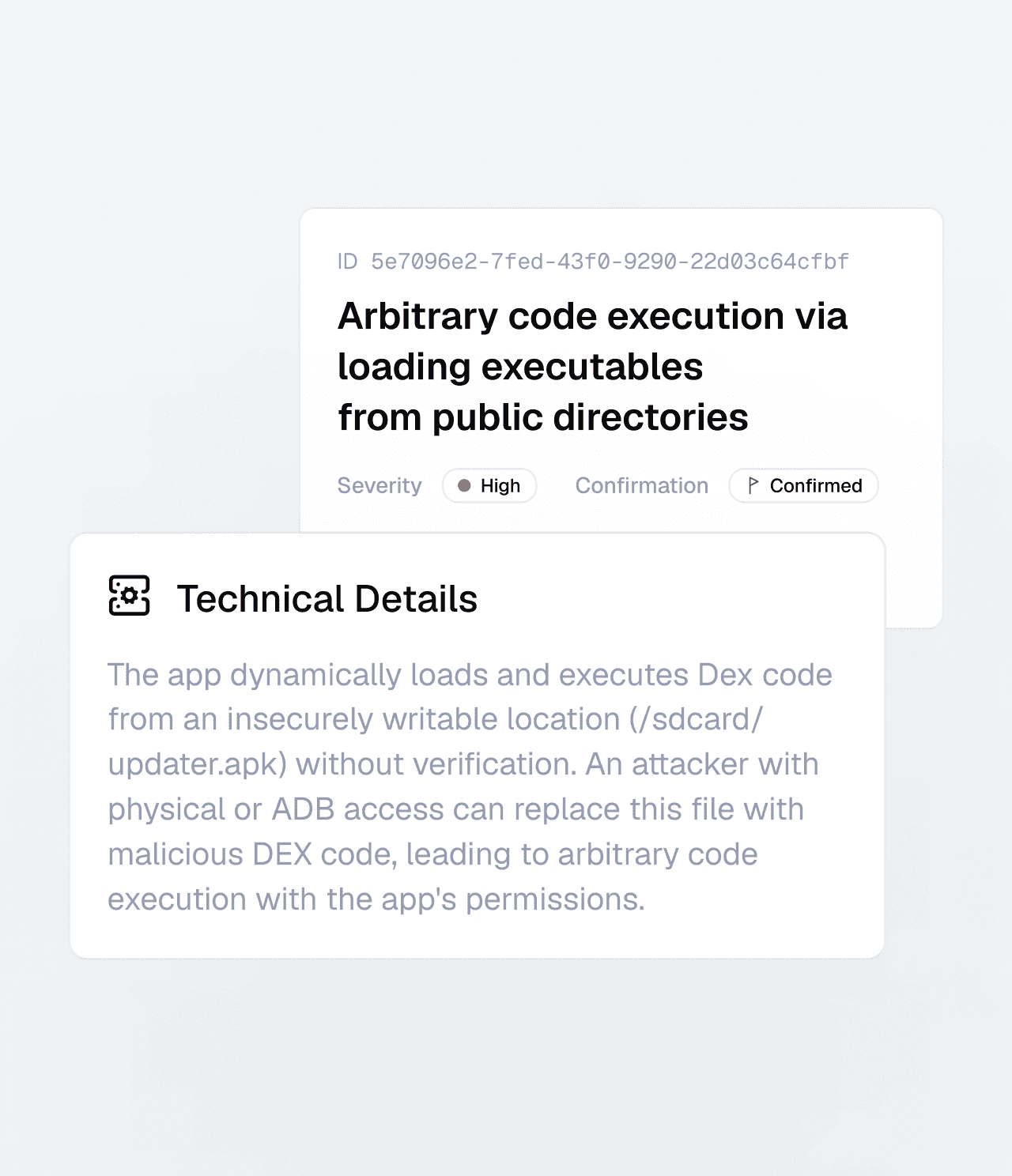
Technical details
How the vulnerability works in this specific code, with the relevant execution path

How to fix
Concrete remediation guidance, specific to the code and context — not a generic reference to a standard
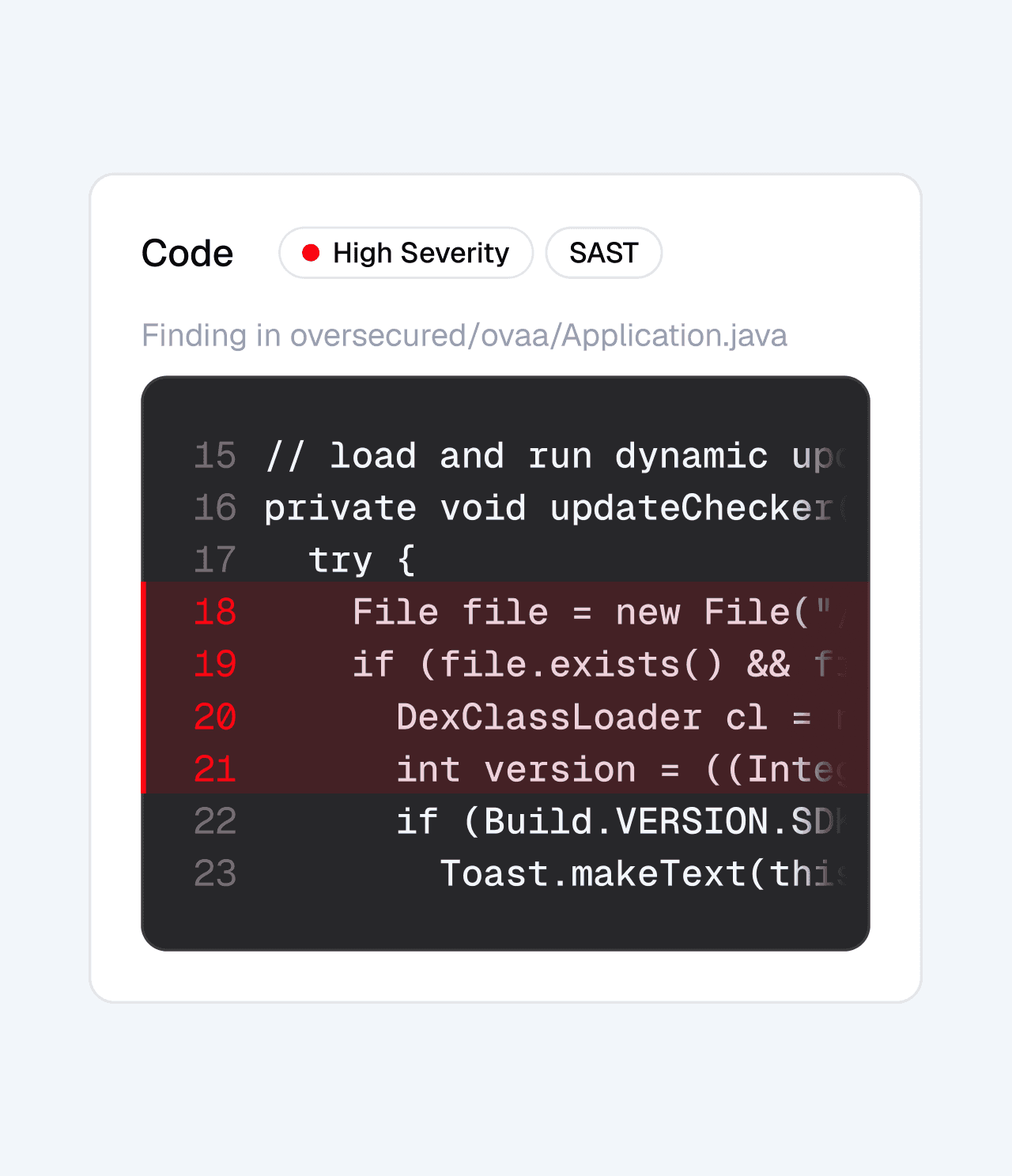
Code snippet
The relevant lines of code, highlighted

Proof of Concept
Full command, deeplink payload, or exploit code to reproduce the issue

Stack trace
The full execution path of the code
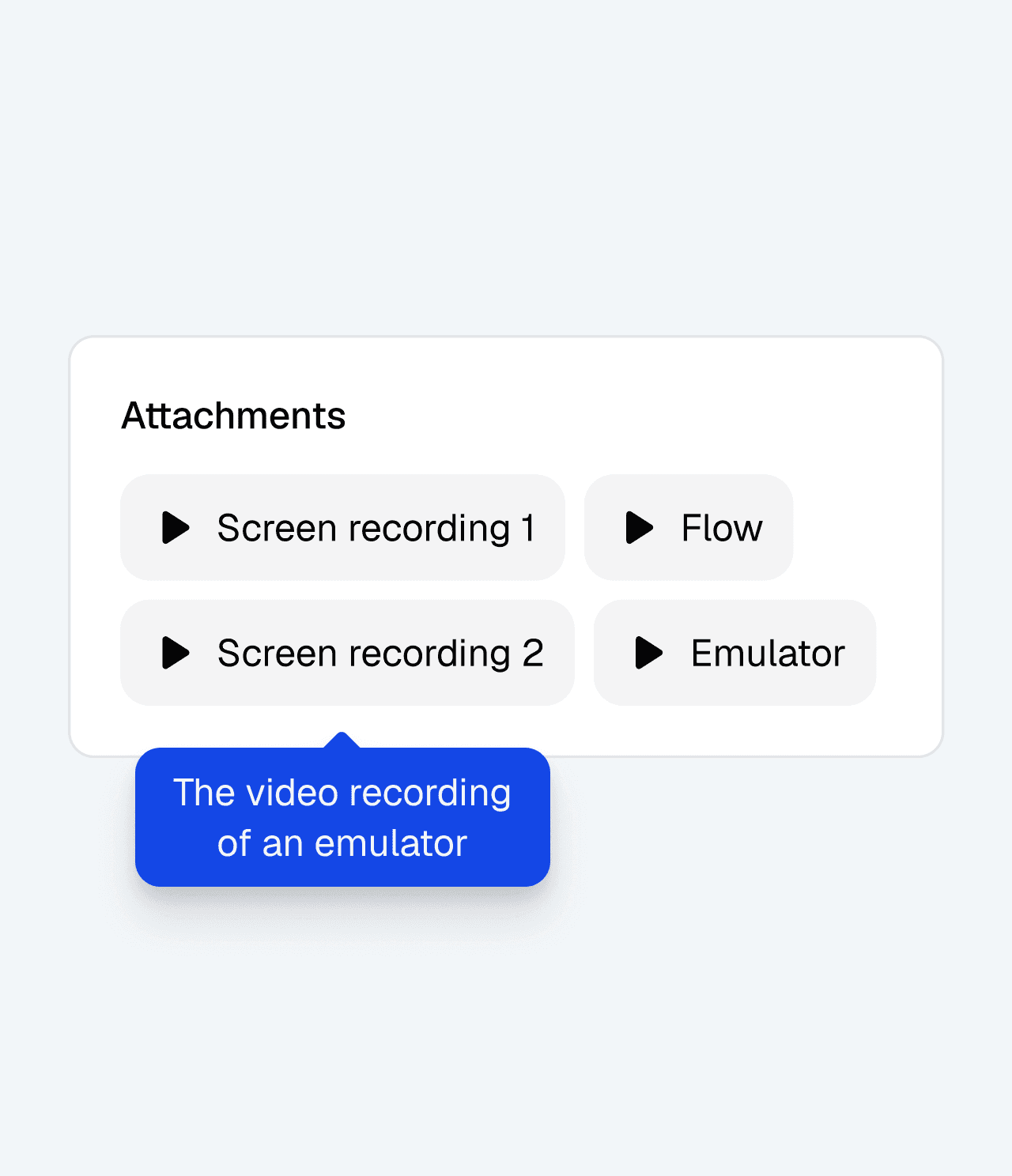
Screencast
The video recording of an emulator showing the vulnerability in action

Business impact
What an attacker could achieve if this is exploited: data theft, account takeover, financial loss

Technical impact
What happens at the system level: which data is exposed, which operations are affected

Technical details
How the vulnerability works in this specific code, with the relevant execution path

How to fix
Concrete remediation guidance, specific to the code and context — not a generic reference to a standard

Code snippet
The relevant lines of code, highlighted
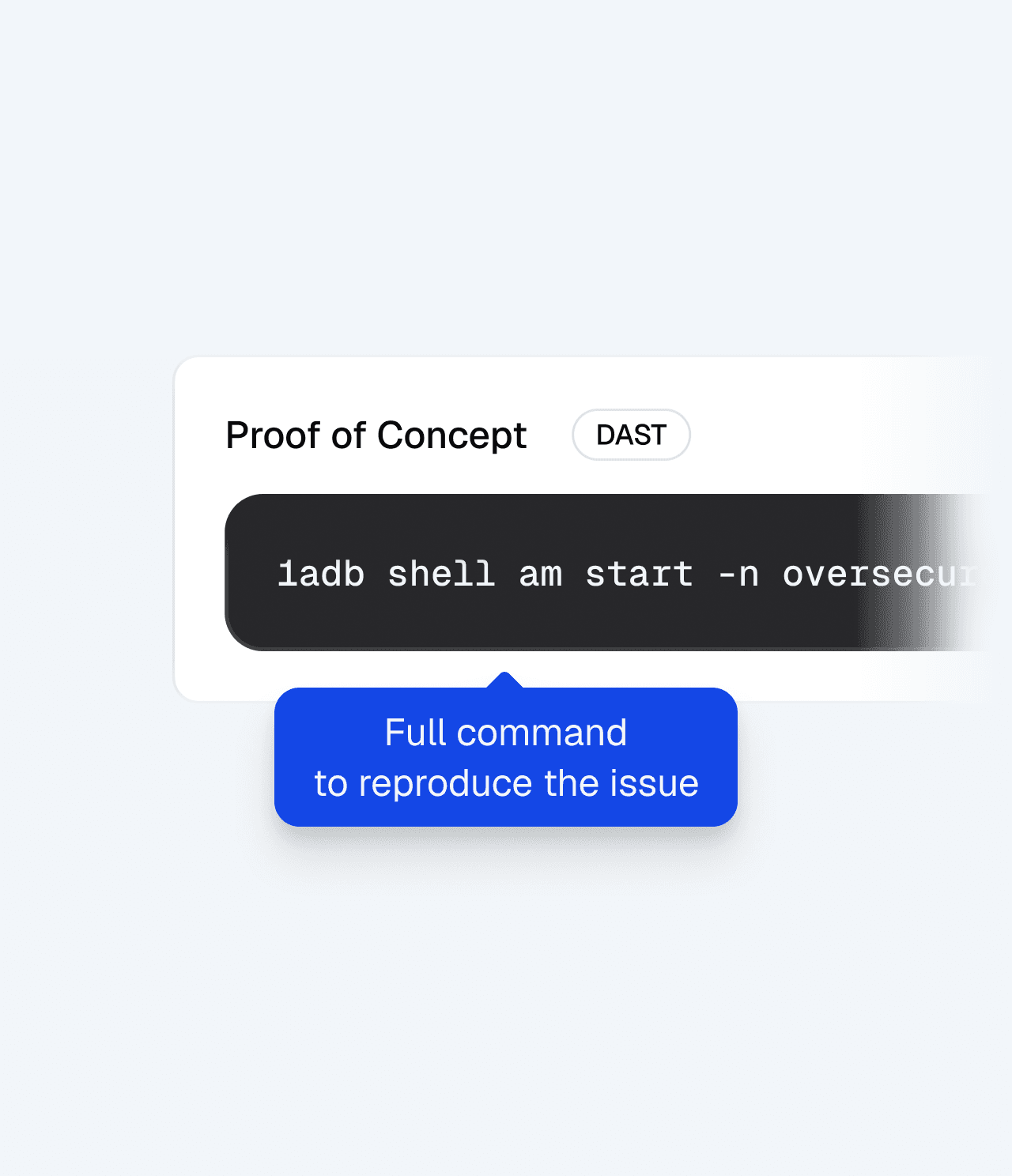
Proof of Concept
Full command, deeplink payload, or exploit code to reproduce the issue

Stack trace
The full execution path of the code

Screencast
The video recording of an emulator showing the vulnerability in action
Multiple analysis modes
in one platform
Multiple analysis modes
in one platform
SAST
Static Analysis
Oversecured traces how untrusted data moves through the app and whether it can lead to real security impact.
For Android - only APKs are required.
For iOS - source code required.
Covers 175+ Android and 85+ iOS vulnerability types.
Each finding includes affected code, severity, impact, and remediation guidance.


DAST
Dynamic Analysis
Oversecured runs your app in a controlled environment and tests real attack paths. It fuzzes deep links, exported components, and inter-app communication to see how the app behaves at runtime.
Prove which vulnerabilities are actually exploitable.
Get a proof of concept, stack traces, video recordings, and clear reproduction steps.
Includes bypasses for common runtime protections.
IAST
Interactive Analysis
Oversecured logs in with your configured test account and scans the protected areas users actually access.
Each login step is recorded with a screencast of the device and a proof-of-concept
Test the app beyond the login screen like payment flows, account settings, private content, and more.


268 categories
53 rules and regulations
Staying compliant
with every app change
Staying compliant
with every app change
Select the frameworks that apply to each app. Oversecured maps every finding to the relevant regulations, so you can see how each release affects your compliance posture.
Select the frameworks that apply to each app. Oversecured maps every finding to the relevant regulations, so you can see how each release affects your compliance posture.
OWASP Mobile Top 10 (2024)
CWE
MITRE ATT&CK for Mobile v18
JSSEC (Japan)
NIAP v1.4
OWASP MASVS v2
CAPEC v3
Google MASA
NIAP v1.4
NIAP v1.4
OWASP Mobile Top 10 (2024)
CWE
MITRE ATT&CK for Mobile v18
JSSEC (Japan)
NIAP v1.4
OWASP MASVS v2
CAPEC v3
Google MASA
NIAP v1.4
NIAP v1.4
PCI DSS v4
PCI MPoC v1.1
DORA (EU)
PSD2 SCA
BNM RMiT (Malaysia)
MAS TRM
CBE (Egypt)
BDDK (Turkey)
BNM RMiT (Malaysia)
HIPAA Security Rule
PCI DSS v4
PCI MPoC v1.1
DORA (EU)
PSD2 SCA
BNM RMiT (Malaysia)
MAS TRM
CBE (Egypt)
BDDK (Turkey)
BNM RMiT (Malaysia)
HIPAA Security Rule
Taint analysis — the engine no other mobile scanner offers
Taint analysis — the engine no other mobile scanner offers
Taint analysis — the engine no other
mobile scanner offers
Most scanners flag dangerous functions.
Oversecured checks whether attacker-controlled data can actually reach them.
01 Tainted Source
Untrusted Input
getIntent()
attacker-controlled · tainted
02 Propagation Through Your App
Your Code
parseInput(data)
flows through · still taited
03 Sensitive Sink
Sensitive GP
Real Vulnerability
db,rawQuerry(sql)
reachable – unvalidated
What it catches that other tools miss
What it catches that
other tools miss
Cross-component data leaks
Cross-component data leaks
Intent injection
Intent injection
Command injection
Command injection
SQL injection
SQL injection
WebView XSS
WebView XSS
Path traversal
Path traversal
SSRF
SSRF
Why this is unique
No other commercial or open-source mobile security tool offers it.
Other pattern matching tools create noise — our taint analysis follows the full data path.
No other commercial or open-source mobile security tool offers it. Pattern matching creates noise. Our taint analysis follows the full data path.
No other commercial or open-source mobile security tool offers it. Pattern matching creates noise. Our taint analysis follows the full data path.
As a result, you get:
No other commercial or open-source mobile security tool offers it. Pattern matching creates noise. Our taint analysis follows the full data path.
No other commercial or open-source mobile security tool offers it. Pattern matching creates noise. Our taint analysis follows the full data path.
Fewer false positives
Deeper vulnerability detection
Complex issues other tools miss
Why teams choose Oversecured

Tests deeper than others
5,500+ custom rules and data-flow analysis help Oversecured find complex vulnerabilities that pattern-matching tools miss.

Shows what’s actually exploitable
Every DAST finding includes a proof of concept and a stack trace showing how the vulnerability is triggered.

Reaches post-login app areas
Oversecured logs into your app automatically and tests authenticated screens, flows, and sensitive functionality.

No Android source code required
Upload an APK, AAB, or APKS. Oversecured decompiles the app and analyzes the reconstructed Java code.

Finds issues in third-party SDKs
Oversecured checks SDKs for known CVEs and vulnerabilities caused by how they’re integrated into your app.

Built to reduce false positives
Data-flow analysis follows the full path from source to sink, helping teams focus on real, actionable findings.

Tests deeper than others
5,500+ custom rules and data-flow analysis help Oversecured find complex vulnerabilities that pattern-matching tools miss.

Shows what’s actually exploitable
Every DAST finding includes a proof of concept and a stack trace showing how the vulnerability is triggered.

Reaches post-login app areas
Oversecured logs into your app automatically and tests authenticated screens, flows, and sensitive functionality.

No Android source code required
Upload an APK, AAB, or APKS. Oversecured decompiles the app and analyzes the reconstructed Java code.

Finds issues in third-party SDKs
Oversecured checks SDKs for known CVEs and vulnerabilities caused by how they’re integrated into your app.

Built to reduce false positives
Data-flow analysis follows the full path from source to sink, helping teams focus on real, actionable findings.

Tests deeper than others
5,500+ custom rules and data-flow analysis help Oversecured find complex vulnerabilities that pattern-matching tools miss.

Shows what’s actually exploitable
Every DAST finding includes a proof of concept and a stack trace showing how the vulnerability is triggered.

Reaches post-login app areas
Oversecured logs into your app automatically and tests authenticated screens, flows, and sensitive functionality.

No Android source code required
Upload an APK, AAB, or APKS. Oversecured decompiles the app and analyzes the reconstructed Java code.

Finds issues in third-party SDKs
Oversecured checks SDKs for known CVEs and vulnerabilities caused by how they’re integrated into your app.

Built to reduce false positives
Data-flow analysis follows the full path from source to sink, helping teams focus on real, actionable findings.
Common mobile security challenges we hear from teams
Common mobile security challenges
we hear from teams
Hard triage
Weak security coverage
Compliance readiness
Continuous security
"Developers need clearer guidance to fix security issues"
Oversecured’s DAST creates exploits for each vulnerability and shows how they are triggered — with proof of concept, impact context, and how-to-fix steps. So your team fixes real risks, not wasting time on theoretical alerts.
Hard triage
Weak security coverage
Compliance readiness
Continuous security
"Developers need clearer guidance to fix security issues"
Oversecured’s DAST creates exploits for each vulnerability and shows how they are triggered — with proof of concept, impact context, and how-to-fix steps. So your team fixes real risks, not wasting time on theoretical alerts.
Hard triage
Weak security coverage
Compliance readiness
Continuous security
"Developers need clearer guidance to fix security issues"
Oversecured’s DAST creates exploits for each vulnerability and shows how they are triggered — with proof of concept, impact context, and how-to-fix steps. So your team fixes real risks, not wasting time on theoretical alerts.
Security that fits into
the pipeline you already have
CLI & MCP integrations
Use Oversecured from the terminal or connect it to your AI agent to scan apps, triage, and set up any workflow.
Access Management
& SSO
Role-based access control for workspace members. SSO via Microsoft Entra ID (live) and Google Workspace.
REST API & Webhooks
Full REST API for custom automation. Webhooks for real-time notifications to Slack, Jira, email, or any endpoint.
Folders & Triage
Organize findings into custom folders. Move confirmed false positives to a dedicated folder so they're excluded from future reports without being deleted.
Report Sharing
Share full reports, individual findings, or compliance exports. Generate links for external reviewers without giving full platform access.
CLI & MCP integrations
Use Oversecured from the terminal or connect it to your AI agent to scan apps, triage, and set up any workflow.
Access Management
& SSO
Access Management & SSO
Role-based access control for workspace members. SSO via Microsoft Entra ID and Google Workspace supported.
REST API & Webhooks
Full REST API for custom automation. Webhooks for real-time notifications to Slack, Jira, and email.
Folders & Triage
Organize findings into custom folders. Move false positives to a dedicated folder so they're excluded from future reports.
Report Sharing
Share full reports, individual findings, or compliance exports without giving full platform access.
More than a vendor.
Your mobile security partner
Work directly with the team behind Oversecured — the researchers who found CVEs in Google, Samsung, TikTok, and others.
Work directly with the team behind Oversecured — the researchers
who found CVEs in Google, Samsung, TikTok, and others.
Onboarding
Dedicated technical account manager
CI/CD integration support
Security team enablement sessions
Ongoing support
Shared Slack channel
Regular check-ins and security reviews
Detection updates from active research
Custom approach
Custom approach
Have custom auth flows, proprietary frameworks,
or unusual IPC mechanisms? Our research team can build
custom detection rules for your scanner instance.
Have custom auth flows, proprietary frameworks, or unusual IPC mechanisms? Our research team can build custom detection rules for your scanner instance.
Have custom auth flows, proprietary frameworks, or unusual IPC mechanisms? Our research team can build custom detection rules for your scanner instance.
What our cutomers are saying
What our cutomers are saying
Security Engineering Leader
"The team at Oversecured comes across as technically strong. During our POC, they helped us review findings and get set up correctly. That technical partnership made a real difference."
Kavak.com
90% faster
Time to security review per release
"The time of security review was reduced from 8-16 hours to ~1 hour in most cases."
Information Security Engineer
"Oversecured reports provide valuable context for potential findings. Oversecured blog posts are some of the most informative and comprehensive documentation of Android application vulnerabilities available."
#1
in Mobile Security
Oversecured ranked #1 in Samsung's mobile vulnerability detection program
CNN's investigation — featuring findings from Oversecured — reveals how one of China's most popular shopping apps exploited Android vulnerabilities to monitor users and bypass phone security
Product Security Engineer
"This sophisticated tool has streamlined the security triaging process, delivering accurate results with a notably low rate of false positives."
Security Engineering Leader
"The team at Oversecured comes across as technically strong. During our POC, they helped us review findings and get set up correctly. That technical partnership made a real difference."
Kavak.com
90% faster
Time to security review per release
"The time of security review was reduced from 8-16 hours to ~1 hour in most cases."
Information Security Engineer
"Oversecured reports provide valuable context for potential findings. Oversecured blog posts are some of the most informative and comprehensive documentation of Android application vulnerabilities available."
#1
in Mobile Security
Oversecured ranked #1 in Samsung's mobile vulnerability detection program
CNN's investigation — featuring findings from Oversecured — reveals how one of China's most popular shopping apps exploited Android vulnerabilities to monitor users and bypass phone security
Product Security Engineer
"This sophisticated tool has streamlined the security triaging process, delivering accurate results with a notably low rate of false positives."




Watch Oversecured find real vulnerabilities in your app
Watch Oversecured find real
vulnerabilities in your app
Book a demo and see taint analysis, authenticated scanning,
and exploit-backed checks in action.
Book a demo and see taint analysis, authenticated scanning, and exploit-backed findings in action.


Security Engineering Leader
"The team at Oversecured comes across as technically strong. During our POC, they helped us review findings and get set up correctly. That technical partnership made a real difference."
Kavak.com
90% faster
Time to security review per release
"The time of security review was reduced from 8-16 hours to ~1 hour in most cases."
Information Security Engineer
"Oversecured reports provide valuable context for potential findings. Oversecured blog posts are some of the most informative and comprehensive documentation of Android application vulnerabilities available."
#1
in Mobile Security
Oversecured ranked #1 in Samsung's mobile vulnerability detection program
CNN's investigation — featuring findings from Oversecured — reveals how one of China's most popular shopping apps exploited Android vulnerabilities to monitor users and bypass phone security
Product Security Engineer
"This sophisticated tool has streamlined the security triaging process, delivering accurate results with a notably low rate of false positives."